A new ClickFix malware campaign is using compromised WordPress websites to spread infostealer malware to unsuspecting visitors. Instead of hosting malicious pages on attacker-controlled domains, the campaign abuses legitimate websites that have already built trust with users.
Security researchers discovered hundreds of infected websites redirecting visitors to fake verification pages. These pages imitate familiar CAPTCHA prompts and instruct users to perform actions that ultimately install malware.
The campaign highlights how attackers increasingly rely on social engineering combined with compromised websites to distribute data-stealing malware.
Attackers Compromise WordPress Websites
The campaign relies on compromised WordPress sites that attackers use as delivery platforms for malicious scripts. Researchers identified hundreds of infected websites across multiple countries, including news portals and public-facing websites.
Once attackers gain access to a website, they inject malicious code that redirects visitors to a fake verification page. This page appears legitimate and mimics common security checks that users encounter when accessing protected websites.
Because the infection occurs on trusted domains, visitors are less likely to suspect malicious activity.
Fake CAPTCHA Prompts Trigger the ClickFix Trick
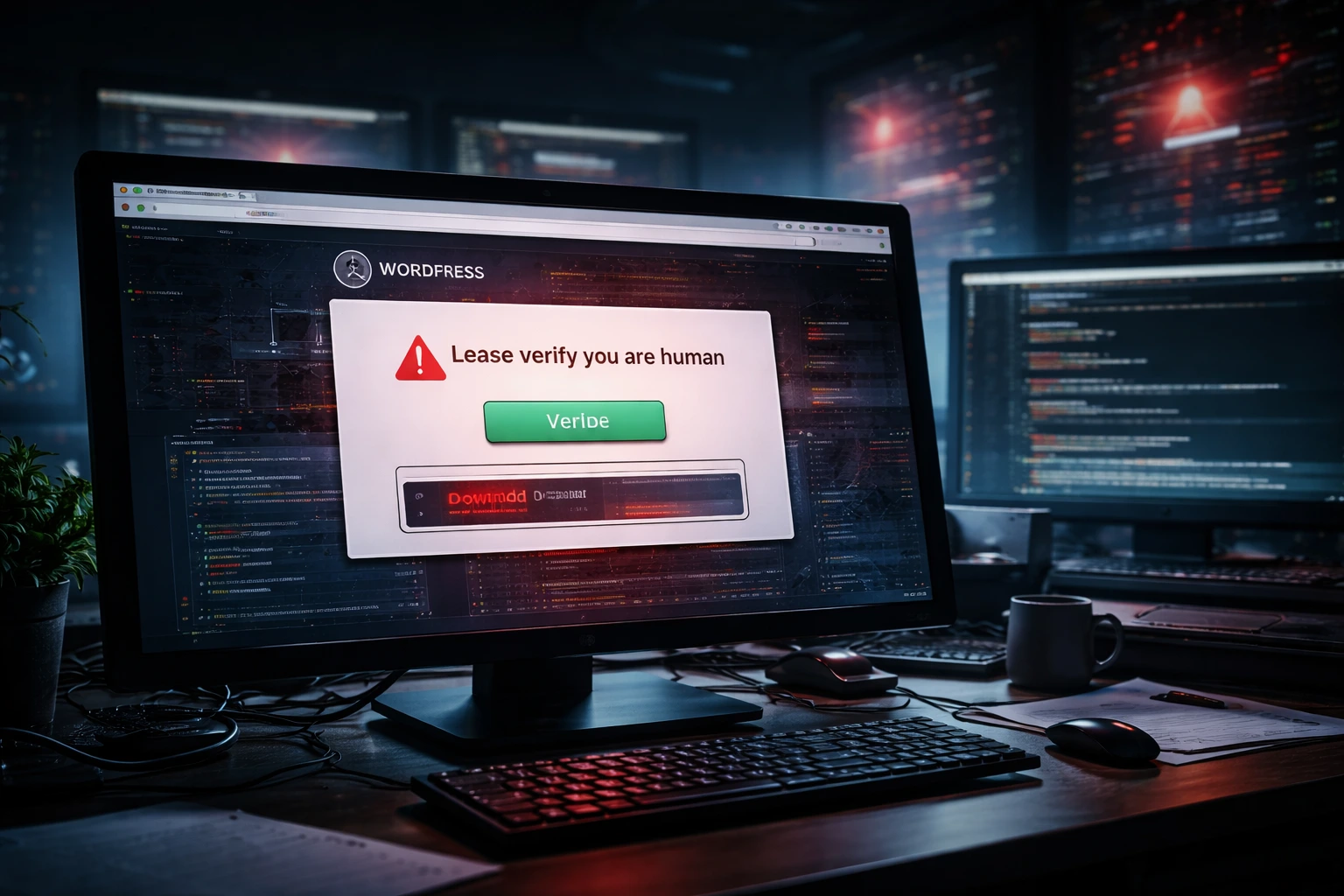
Visitors who land on a compromised site encounter a page that resembles a CAPTCHA verification check. The message claims the visitor must complete a short verification process before continuing to the site.
Instead of simply clicking a checkbox, users are instructed to follow a series of steps that appear harmless. The instructions guide them to copy and run a command on their system.
This technique, known as ClickFix, manipulates users into executing malicious commands themselves. Once the command runs, the attacker gains a foothold on the victim’s computer.
Infostealer Malware Targets Sensitive Data
After the malicious command executes, the system downloads infostealer malware. These types of malware focus on collecting valuable information stored on the victim’s device.
Infostealers commonly search for saved browser credentials, authentication tokens, and session cookies. They may also attempt to access cryptocurrency wallet data and other sensitive information stored on the system.
The stolen data is then transmitted to attacker-controlled servers, where it can be used for account takeovers, financial fraud, or further cyberattacks.
Stolen Credentials May Enable the Website Compromises
Researchers investigating the campaign believe attackers gained access to the WordPress websites through stolen administrator credentials rather than exploiting a single shared vulnerability.
If attackers obtain valid login information, they can access the site’s administration panel and inject malicious scripts directly into the site. This allows them to turn legitimate websites into malware distribution platforms.
Weak passwords, reused credentials, and previously compromised accounts can make websites vulnerable to this type of intrusion.
Conclusion
The ClickFix malware campaign demonstrates how attackers continue to combine social engineering with compromised websites to spread infostealer malware. By abusing trusted WordPress sites and disguising the attack as a CAPTCHA verification process, cybercriminals can trick users into installing malware themselves.
These tactics allow attackers to bypass many traditional security defenses because the malicious activity originates from legitimate domains. As a result, unsuspecting visitors may encounter malware while browsing otherwise trusted websites.
Website administrators must secure their accounts and monitor their sites for suspicious changes. At the same time, users should remain cautious when websites ask them to run commands or perform unusual verification steps.

0 responses to “ClickFix Malware Campaign Hijacks WordPress Sites to Deliver Infostealers”