Tag: Clickfix
-
A new ClickFix malware campaign is using compromised WordPress websites to spread infostealer malware to unsuspecting visitors. Instead of hosting malicious pages on attacker-controlled domains, the campaign abuses legitimate websites that have already built trust with users. Security researchers discovered hundreds of infected websites redirecting visitors to fake verification pages. These pages imitate familiar CAPTCHA…
-
Security researchers discovered a ClickFix DNS attack that delivers malware using a normal Windows diagnostic command. Instead of downloading a file, victims unknowingly pull malicious code directly through DNS queries. The technique hides the payload inside ordinary network traffic and reduces the chance of detection. Users tricked into running commands The campaign relies on social…
-
Researchers discovered a ClickFix crypto attack that tricks cryptocurrency users into executing malicious browser code. Attackers promote fake profit methods in Pastebin comments and convince victims to run JavaScript manually. Once executed, the script silently alters crypto swap transactions and redirects funds to attacker wallets. Fake arbitrage guides spread the scam The operation starts with…
-
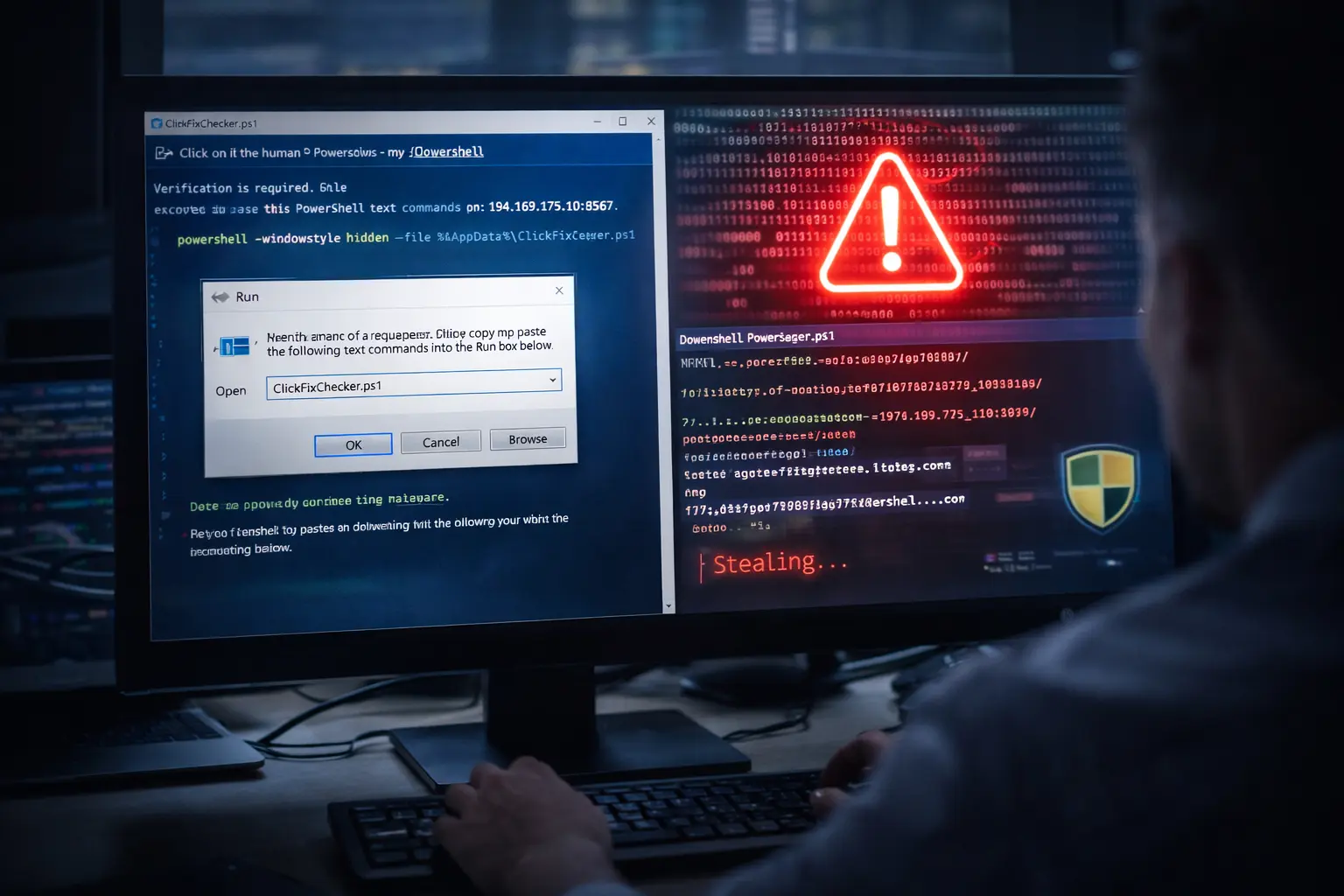
A ClickFix access broker campaign has emerged that targets Windows users through deceptive interaction rather than direct exploitation. Attackers rely on carefully crafted prompts that persuade victims to run malicious commands themselves. This approach allows the attackers to bypass many traditional defenses without exploiting software flaws. The campaign shows how threat actors increasingly depend on…
-
ClickFix App-V malware attacks show how threat actors continue to refine social engineering tactics. Attackers now abuse trusted Windows components to push malware onto victim systems. They rely on fake human-verification prompts and Microsoft’s Application Virtualization framework to bypass security controls. This method succeeds because it persuades users to trigger the attack themselves. The campaign…
-
A new ClickFix malware campaign uses fake Windows Blue Screen of Death (BSOD) screens to trick users into infecting their own systems. Attackers display convincing crash messages and then guide victims through “fix” steps that secretly install malware. The technique relies on social engineering rather than exploits, which allows it to bypass many traditional security…
-
Security researchers have identified a new cybercrime service called ErrTraffic that is accelerating the spread of ClickFix attacks. The platform enables attackers to abuse fake browser glitches and error messages to manipulate users into executing malicious commands themselves. Instead of relying on exploits or drive-by downloads, this approach focuses entirely on social engineering. The emergence…
-
A deceptive malware campaign is gaining attention for its use of fake Windows Update screens. Attackers employ a social-engineering trick that convinces users to execute harmful commands. The ClickFix attack highlights how familiar system visuals can be weaponised with very little technical friction. How the ClickFix attack fools users When victims land on a compromised…
-
ClickFix ransomware has evolved, now exploiting AI-generated summaries to compromise organizations. This new tactic allows attackers to access sensitive data faster. Security experts warn that the combination of AI tools and ransomware increases the risk of targeted attacks. How ClickFix Uses AI Cybercriminals leverage AI summarization tools to gather intelligence. They analyze large volumes of…
-
Restrict command-line tools is Microsoft’s latest security advice after a surge of phishing campaigns. The tech giant warns that attackers are tricking users into copying malicious code into Windows Run, PowerShell, or Terminal. Once executed, these commands launch malware, steal data, and bypass defenses. Microsoft stresses that restricting these tools can block one of today’s…