Infinity Stealer macOS malware is spreading through a deceptive technique that tricks users into infecting their own devices. Attackers rely on fake verification prompts that appear legitimate at first glance. This approach allows the malware to bypass traditional protections without exploiting software flaws.
Security researchers identified this campaign as a shift in macOS threats. Instead of targeting vulnerabilities, attackers focus on manipulating user behavior. As a result, even cautious users can become victims if they follow the instructions.
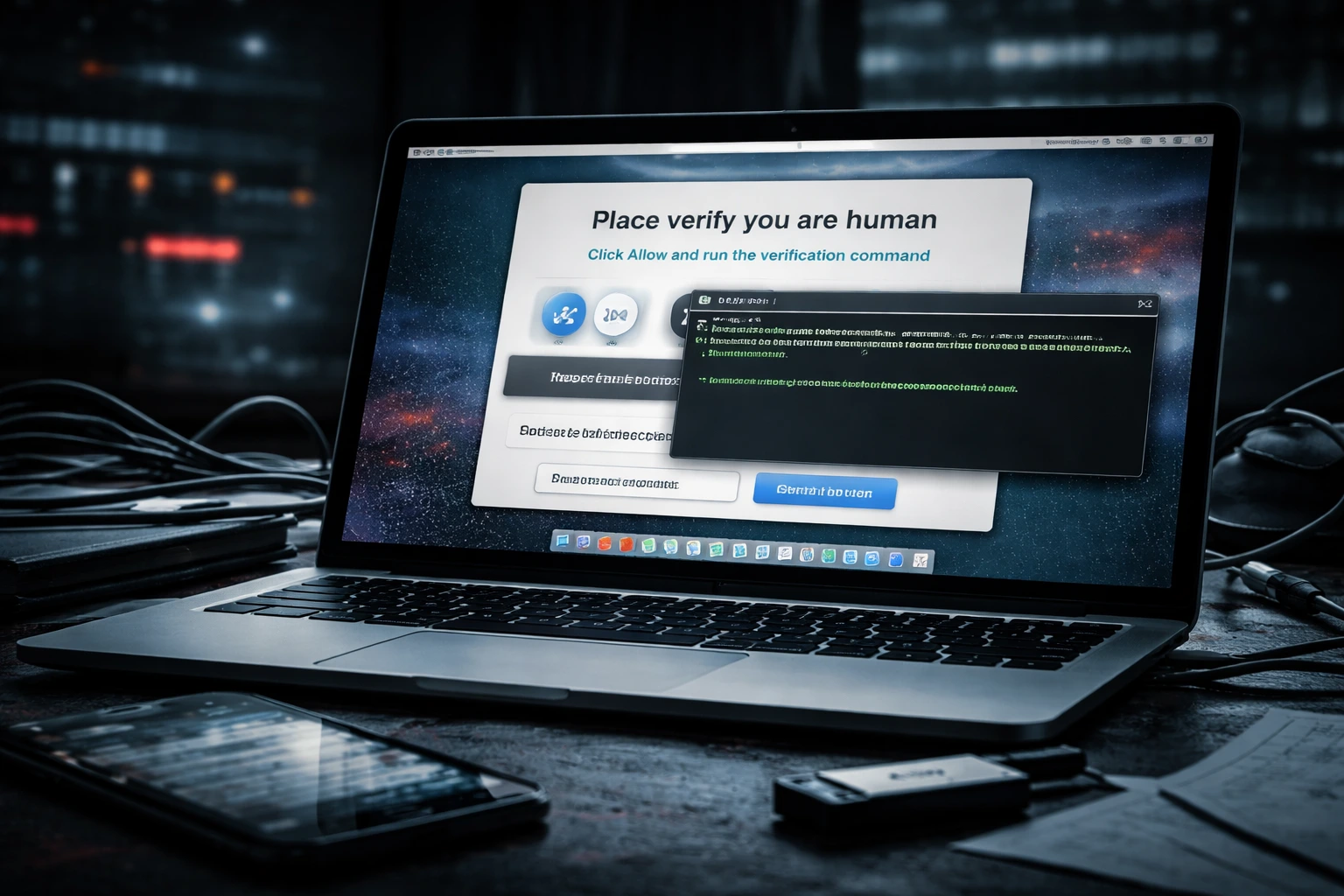
Fake verification prompts trigger infection
Infinity Stealer macOS campaigns use fake CAPTCHA-style pages to lure victims. These pages imitate trusted services and display a message that requires user action to continue.
Victims are instructed to open the Terminal and paste a command. Once executed, the command silently downloads and launches the malware. This process makes the attack appear harmless while giving full control to the malicious script.
Because the user initiates the action, standard browser protections do not block the attack.
Multi-stage execution helps evade detection
Infinity Stealer macOS uses a multi-stage infection chain to remain hidden. The initial command triggers a script that downloads a secondary payload and runs it in the background.
The malware is written in Python and compiled into a native binary. This makes analysis and detection more difficult for security tools. Before collecting data, the malware checks its environment to avoid running in virtual machines or analysis systems.
These techniques allow it to operate quietly while reducing the chance of detection.
Malware targets credentials and sensitive files
Infinity Stealer macOS is designed to collect a wide range of sensitive data from infected devices. It focuses on both personal and development-related information stored locally.
The malware can access browser credentials, keychain data, and cryptocurrency wallet files. It also scans for plaintext secrets in configuration files and development environments.
In some cases, it captures screenshots to gather additional context. All collected data is then sent to attacker-controlled infrastructure.
ClickFix technique increases effectiveness
Infinity Stealer macOS highlights the growing use of the ClickFix method in malware campaigns. This technique relies entirely on user interaction instead of exploiting technical weaknesses.
Attackers use convincing prompts to guide users through the infection process. This makes the attack more difficult to detect and block using traditional security measures.
As this method continues to evolve, similar campaigns are likely to become more common.
Conclusion
Infinity Stealer macOS shows how attackers are shifting toward social engineering to deliver malware. By convincing users to execute commands themselves, threat actors bypass many existing defenses.
This trend increases the importance of user awareness. Avoiding unknown commands and questioning unexpected prompts can prevent infections and reduce risk.

0 responses to “Infinity Stealer macOS malware targets users through ClickFix lures”