Category: Cyber Security
-
Law enforcement agencies have dismantled a large cybercrime platform that relied on infected home routers worldwide. The operation targeted the SocksEscort proxy network, a service that allowed criminals to hide their activity behind residential internet connections. Investigators say the network enabled a wide range of illegal operations. Attackers used it to disguise fraud campaigns, credential…
-
Google has released emergency updates to fix two security flaws in the Chrome browser. Attackers exploited both vulnerabilities before patches became available. The Chrome zero-day flaws appeared in real-world attacks. Google confirmed that threat actors used the bugs before the company released the fixes. Security experts now urge users to update Chrome immediately. Installing the…
-
Cybercriminals often exploit trending topics to spread malware. This year’s Academy Awards provide a perfect lure. Researchers discovered a campaign that targets users searching for downloads of Best Picture nominees. Attackers use fake movie download pages to deliver malicious files. Victims believe they are downloading Oscar-nominated films. Instead, they install malware designed to steal cryptocurrency…
-
Authorities shut down a major residential proxy network used by cybercriminals. The service, known as SocksEscort, routed internet traffic through compromised home routers. This method made malicious activity appear to originate from ordinary household connections. Many security systems struggled to detect these attacks. The takedown highlights the growing threat of residential proxy infrastructure. Criminal groups…
-
Autonomous AI systems are becoming more common inside corporate environments. Companies increasingly rely on these agents to automate tasks such as data analysis, internal communication, and software development. However, new research shows that these systems can introduce unexpected cybersecurity risks when they operate with broad access to internal tools. Recent experiments revealed how rogue AI…
-
Security researchers have uncovered a technique that allows malware to hide inside corrupted ZIP archives and bypass antivirus detection. The discovery highlights a weakness in how many security tools process compressed files. By altering archive metadata, attackers can trick scanning engines into skipping the malicious content inside the file. The method is known as Zombie…
-
A major Quittr app leak has exposed sensitive information belonging to more than 600,000 users. The mobile app was designed to help people stop watching pornography and track recovery progress. Security researchers discovered that the app’s backend database was accessible because of a configuration error. The exposed system stored highly personal data related to users’…
-
The Handala hackers have claimed responsibility for cyberattacks targeting two multinational companies, Verifone and Stryker. The group is widely believed to have ties to Iran-aligned cyber networks. The attackers posted statements on their online channels describing the operations. They framed the attacks as retaliation linked to geopolitical tensions in the Middle East. Security analysts say…
-
A suspected Portugal spy campaign is targeting messaging accounts used by government officials, diplomats, and military personnel. Portuguese intelligence authorities warned that attackers are attempting to compromise accounts on secure communication platforms such as WhatsApp and Signal. The campaign appears to focus on gaining access to individual user accounts rather than breaking the encryption of…
-
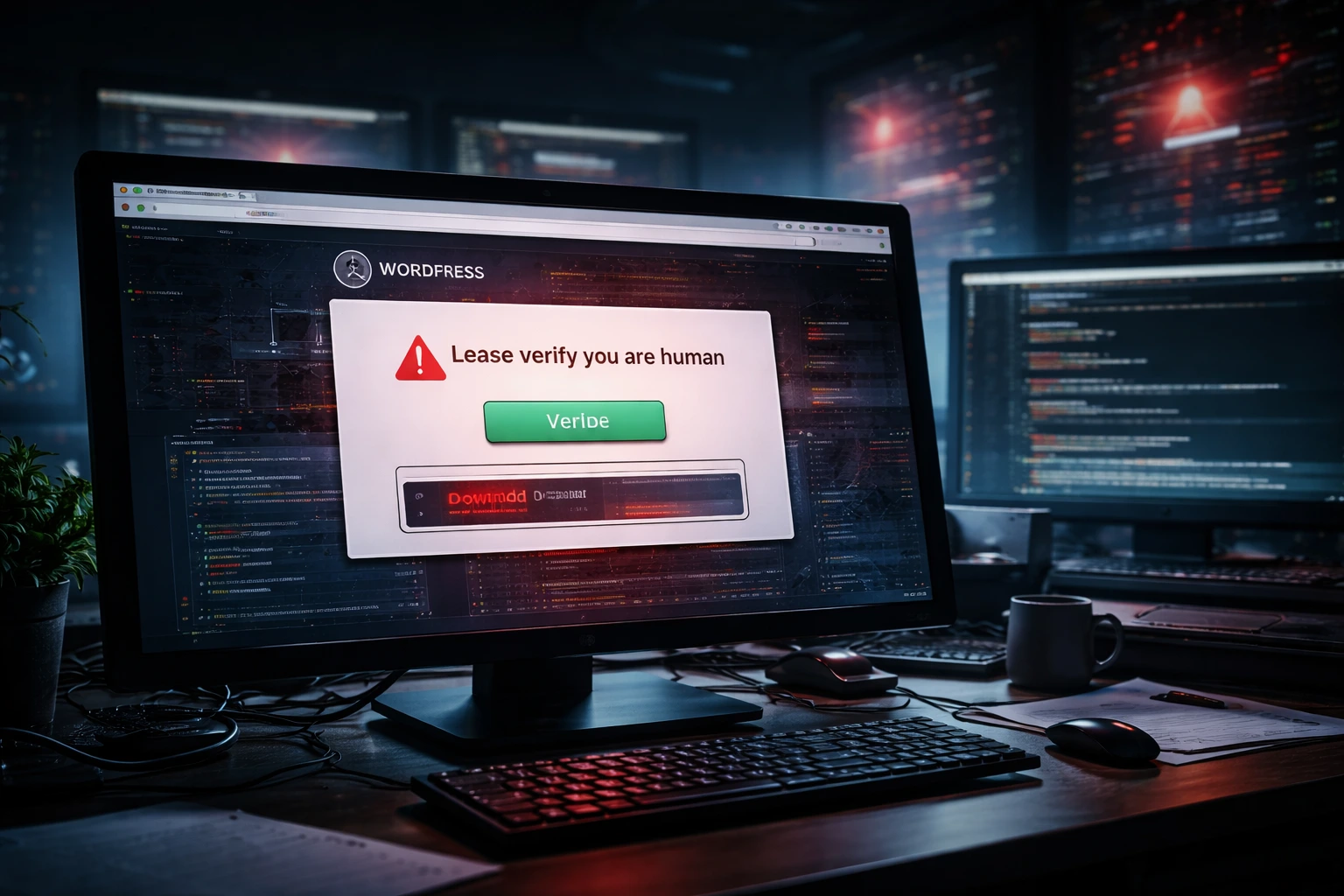
A new ClickFix malware campaign is using compromised WordPress websites to spread infostealer malware to unsuspecting visitors. Instead of hosting malicious pages on attacker-controlled domains, the campaign abuses legitimate websites that have already built trust with users. Security researchers discovered hundreds of infected websites redirecting visitors to fake verification pages. These pages imitate familiar CAPTCHA…