Category: Cyber Security
-
Telnyx PyPI malware has surfaced in a supply chain attack that used a trusted Python package to deliver a hidden payload. Attackers embedded malicious code inside WAV audio files to avoid detection and target developer environments. As a result, the incident shows how attackers continue to abuse open-source distribution channels with more advanced evasion techniques.…
-
GitHub VS Code malware campaigns are targeting developers through fake security alerts posted across repositories. Attackers use urgency and familiar tools to push users toward malicious downloads. The activity shows how developer platforms are becoming direct entry points for social engineering attacks. Fake vulnerability alerts appear at scale Attackers are posting fake Visual Studio Code…
-
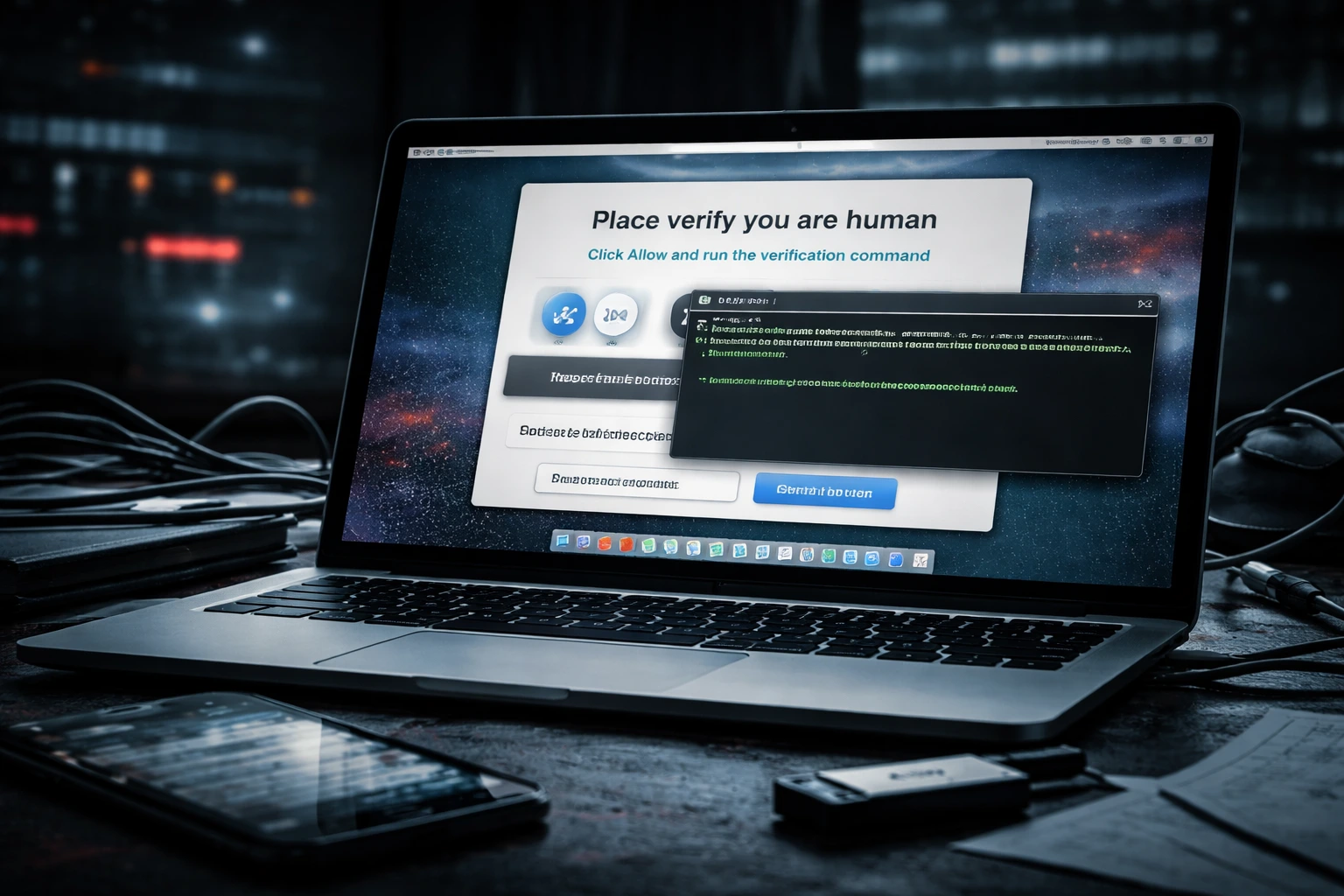
Infinity Stealer macOS malware is spreading through a deceptive technique that tricks users into infecting their own devices. Attackers rely on fake verification prompts that appear legitimate at first glance. This approach allows the malware to bypass traditional protections without exploiting software flaws. Security researchers identified this campaign as a shift in macOS threats. Instead…
-
The Kash Patel email hack is gaining attention after an Iran-linked group claimed it breached the FBI director’s personal account. The incident highlights how high-profile individuals remain targets for politically motivated cyber activity. Hackers associated with the group known as Handala said they accessed Patel’s personal email and released selected materials online. The claim appeared…
-
The Citrix NetScaler vulnerability is exposing thousands of systems to potential attacks. Security researchers identified tens of thousands of internet-facing instances that remain accessible and at risk. These systems support a large number of web services, which increases the potential impact. As a result, a single unpatched flaw could affect critical infrastructure across multiple regions.…
-
The AnimePlay app takedown shows how quickly piracy platforms can grow and how fast enforcement can respond. Authorities shut down the app after it reached millions of users who streamed copyrighted anime without authorization. The case highlights the increasing scale of both illegal streaming services and the efforts to stop them. Major piracy platform taken…
-
The Windows 11 KB5079391 update focuses on practical improvements that enhance both security and usability. It introduces changes to Smart App Control and refines several core system features, giving users more control without adding complexity. This release continues Microsoft’s approach of delivering steady, incremental upgrades. Smart App Control becomes more flexible The Windows 11 KB5079391…
-
Exposed API keys continue to create one of the most overlooked security risks online. Stanford researchers uncovered thousands of active credentials sitting in public view, giving attackers a direct path into critical systems. As APIs power more applications, small mistakes in credential handling now carry serious consequences. Large-scale exposure across the web Researchers scanned millions…
-
PolyShell attacks are exposing weaknesses across Magento environments. Attackers are exploiting a flaw that allows file uploads without proper validation. This creates a direct path to compromise for many online stores. The scale of exposure shows how quickly unpatched systems become targets. Unauthenticated file upload enables entry The vulnerability exists in Magento’s API handling of…
-
Citrix NetScaler vulnerabilities have triggered urgent action across enterprise environments. The flaws affect systems that handle authentication and traffic control, which makes them high-value targets. Citrix has urged administrators to apply patches immediately to reduce exposure. These systems often sit at the edge of networks, where they manage access to internal services. Memory flaw exposes…